Note: This article was based on OpenOffice 3. Since this article was written, OpenOffice version 4 has been released. Click here to read the newer OpenOffice 4 article.
A client recently asked me if I knew of any alternative to Microsoft Office. As a firm believer in open-source software, I told him about OpenOffice.org 3 from Oracle. It is a complete office software suite with a word processor, spreadsheet, multimedia presentation, graphics, and database programs.
OpenOffice.org is Java-based and requires it to be installed. It is compatible with other commercial office software and can read/write various file formats. XSLT and StarOffice formats are supported, but you will need to choose the custom installation to enable these filters. You can also expand the functionality of OpenOffice.org by using third party extensions. And you can also export to PDF in all of the applications. And best of all, it's free.
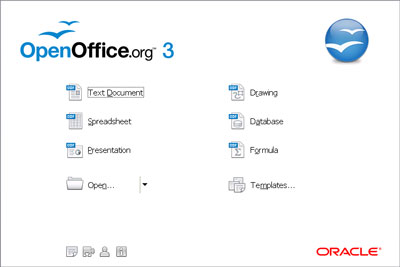
OpenOffice.org 3's main screen
Programs included in OpenOffice.org
Writer
Writer lets you design and produce text documents that can include graphics, tables, or charts. You can then save the documents in a variety of formats, including the standardized OpenDocument format (ODF), Microsoft Word .doc format, or HTML. And you can easily export your document to the Portable Document Format (PDF).
Calc
Calc is a spreadsheet application that you can use to calculate, analyze, and manage your data. You can also import and modify Microsoft Excel spreadsheets.
Impress
Impress lets you create professional slide shows that can include charts, drawing objects, text, multimedia, and a variety of other items. If you want, you can even import and modify Microsoft PowerPoint presentations.
Draw
Draw lets you create simple and complex drawings and export them in a number of common image formats. You can also insert tables, charts, formulas, and other items created in OpenOffice.org programs into your drawings.
Base
With Base, you can access data that is stored in a wide variety of database file formats. Base natively supports some flat file database formats, such as the dBASE format. You can also use Base to connect to external relational databases, such as databases from MySQL or Oracle.
Math
Math provides numerous operators, functions, and formatting assistants to help you create formulas.
OpenOffice.org 3 is available for Windows, Linux, and Mac operating systems. For more information on OpenOffice.org 3, please visit their website OpenOffice.org.
667acf80-c8e5-4745-abe8-b632cf367d7c|1|5.0|96d5b379-7e1d-4dac-a6ba-1e50db561b04